Console: Compliance
Compliance reports
Section titled “Compliance reports”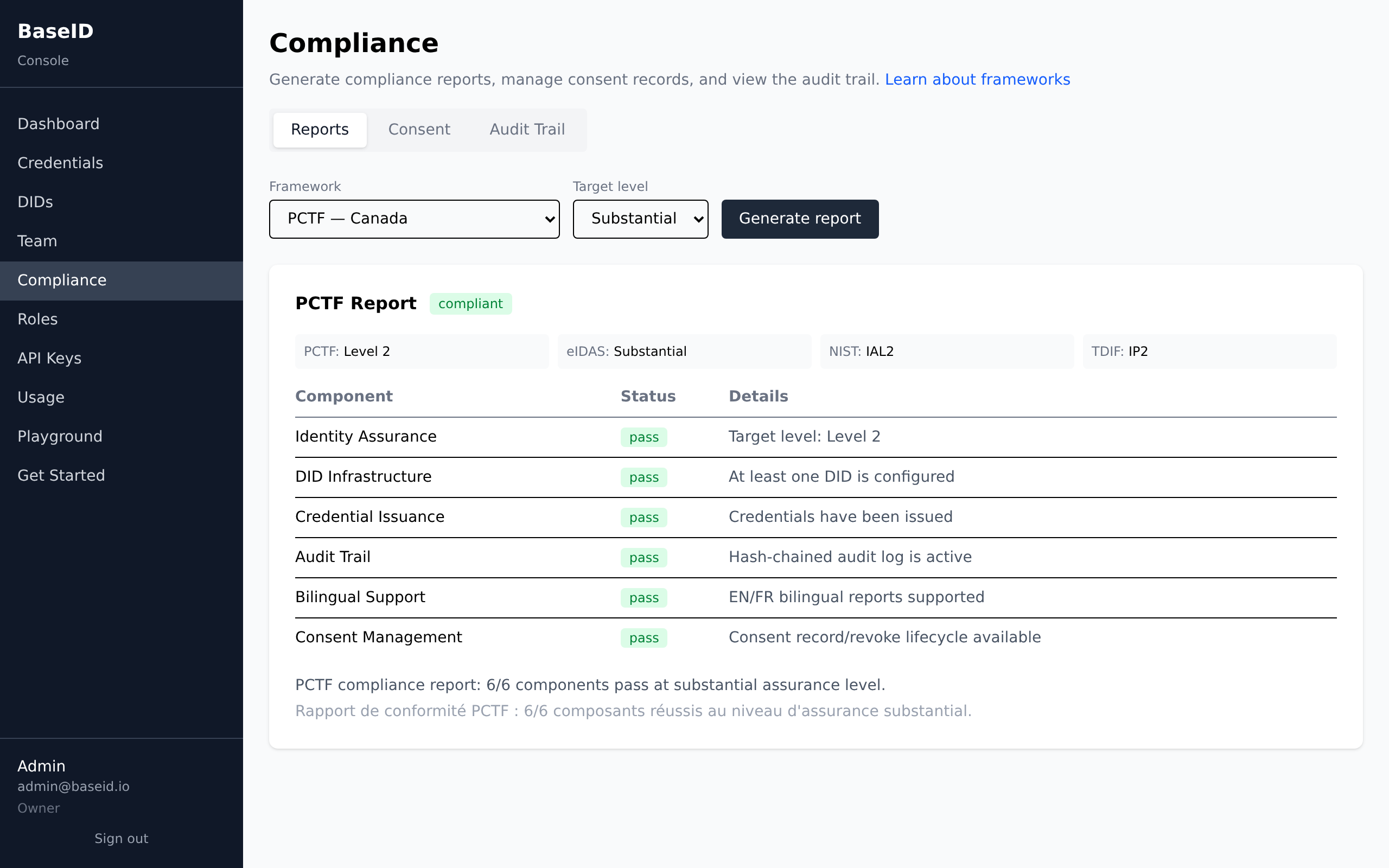
Generate a compliance assessment against any of 7 supported frameworks.
Frameworks
Section titled “Frameworks”| Framework | Region | What it covers |
|---|---|---|
| PCTF | Canada | Pan-Canadian Trust Framework. Identity assurance levels (1-3), consent management, bilingual EN/FR, audit trails. |
| eIDAS 2.0 | EU | European Digital Identity. PID data model, Level of Assurance (Low/Substantial/High), QEAA, trust lists. |
| HAIP | Global | High Assurance Interoperability Profile for OpenID4VC. Credential format constraints (SD-JWT + mDL), algorithm constraints (ES256/EdDSA). |
| NIST 800-63 | US | Identity Assurance Levels (IAL1-3), Authentication Assurance Levels. Federal identity proofing standard. |
| TDIF | Australia | Trusted Digital Identity Framework. Identity Proofing levels (IP1-3), accreditation requirements. |
| MOSIP | Africa/Asia | Modular Open Source Identity Platform. Offline QR verification, low-connectivity credential exchange. |
| DIATF | UK | Digital Identity and Attributes Trust Framework. Service roles, ISO 17065 certification. |
Assurance levels
Section titled “Assurance levels”Reports evaluate your setup against a target assurance level:
| Level | PCTF | eIDAS | NIST | TDIF | Meaning |
|---|---|---|---|---|---|
| Low | Level 1 | Low | IAL1 | IP1 | Basic identity assertion. Self-declared, minimal verification. |
| Substantial | Level 2 | Substantial | IAL2 | IP2 | Verified identity. Government-issued ID, database checks. |
| High | Level 3 | High | IAL3 | IP3 | In-person or biometric verification. Highest confidence. |
Report components
Section titled “Report components”Each report checks several components and marks them as:
- Pass — fully compliant
- Warn — partially compliant or no data yet
- Fail — non-compliant (action needed)
Consent management
Section titled “Consent management”
The Consent tab tracks data-sharing agreements:
- Subject — the person whose data is being shared (DID or identifier)
- Recipient — who receives the data
- Purpose — why the data is being shared (e.g., “age verification”)
- Elements — which data fields are shared (e.g., dateOfBirth, age_over_18)
- Status — active, expired, or revoked
Revoking consent
Section titled “Revoking consent”Revoking consent records the withdrawal but does not retroactively invalidate credentials already shared. It serves as an audit record that consent was withdrawn.
Audit trail
Section titled “Audit trail”
The Audit tab shows a tamper-evident log of all actions in your tenant. Each entry is hash-chained to the previous one, making it detectable if entries are modified or deleted.
Filter by action type to find specific events (e.g., all credential issuances, all team changes).
See the Compliance API reference for programmatic usage.
See also
Section titled “See also”- Compliance Frameworks concept — all 7 frameworks in depth
- Compliance API — programmatic report generation
- Security Model concept — audit trail architecture